
What Is the Common Vulnerability Scoring System?
The Common Vulnerability Scoring System (CVSS) is the industry standard for rating the severity of security vulnerabilities. Security teams, vulnerability management platforms, and regulatory frameworks like NIS-2 rely on CVSS scores to prioritize remediation. Version 4.0, published by the FIRST (Forum of Incident Response and Security Teams), replaces CVSS v3.1 with significant structural improvements.
CVSS scores range from 0.0 to 10.0, where higher values indicate greater severity. Every CVE entry in the National Vulnerability Database and in our CVE Database includes a CVSS score that helps organizations decide which vulnerabilities to fix first.
Why Was CVSS v4.0 Needed?
CVSS v3.1 served the industry well since 2019, but it had known limitations:
- Score inflation: Many vulnerabilities clustered at HIGH and CRITICAL, making prioritization difficult.
- Limited threat context: The Base Score alone did not reflect whether a vulnerability was actively exploited.
- Binary scope metric: The Scope metric in v3.1 was notoriously difficult to apply consistently.
- No supplemental context: There was no standardized way to capture additional risk factors like automatable exploitation or safety impact.
These gaps meant that security teams often needed external data sources — like the CISA KEV catalog or EPSS scores — to make informed decisions. CVSS v4.0 addresses many of these shortcomings directly.
The Four Metric Groups in CVSS v4.0
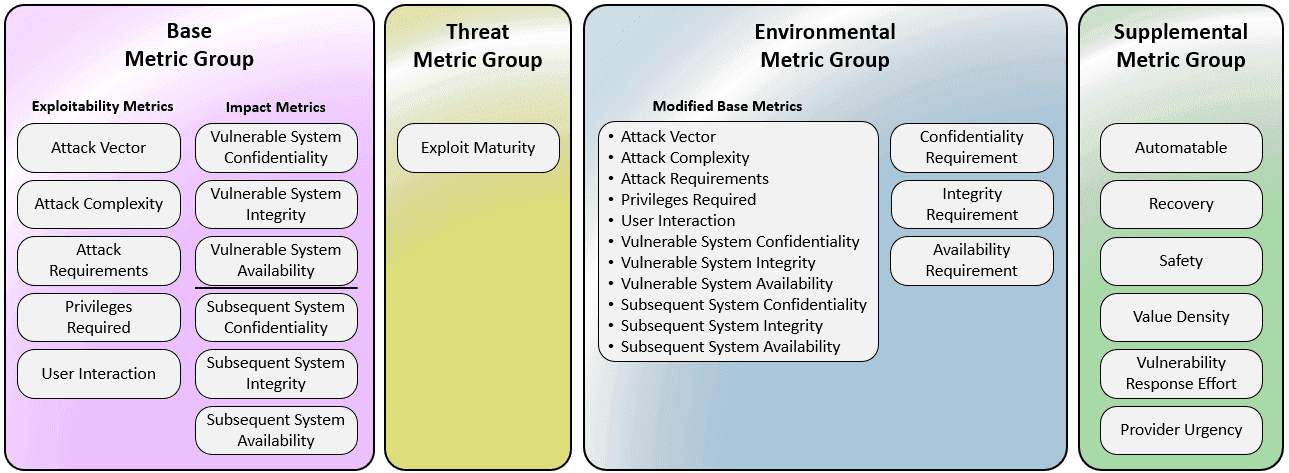
CVSS v4.0 organizes vulnerability scoring into four distinct metric groups, each serving a specific purpose:
Base Metric Group
The Base metrics capture the intrinsic, unchanging properties of a vulnerability. They are split into two categories:
Exploitability Metrics describe how the vulnerability can be attacked:
- Attack Vector (Network, Adjacent, Local, Physical)
- Attack Complexity (Low, High)
- Attack Requirements — new in v4.0, replaces parts of the old Scope metric
- Privileges Required (None, Low, High)
- User Interaction (None, Passive, Active) — v4.0 distinguishes passive from active interaction
Impact Metrics describe the consequences of successful exploitation, now separately scored for the vulnerable system and any downstream systems:
- Confidentiality, Integrity, and Availability impact on the Vulnerable System
- Confidentiality, Integrity, and Availability impact on Subsequent Systems
This separation replaces the binary Scope metric from v3.1 with a more nuanced model that independently measures impact on the exploited component versus connected systems.
Threat Metric Group
The Threat metrics — renamed from "Temporal" in v3.1 — adjust the score based on the current threat landscape. The key metric is Exploit Maturity, which indicates whether functional exploit code exists and whether the vulnerability is being actively exploited in the wild.
This is where CVSS v4.0 connects directly to real-world threat intelligence. A vulnerability with a high Base Score but no known exploit will score lower than one that is actively used in attack surface management scans and darknet monitoring findings.
Environmental Metric Group
The Environmental metrics allow organizations to customize the score based on their specific infrastructure. They include:
- Modified Base Metrics: Override any Base metric to reflect local conditions (e.g., if network access is restricted by firewalls)
- Confidentiality, Integrity, and Availability Requirements: Indicate how critical the affected system is to your organization
For example, a vulnerability in a public-facing web server scores differently than the same vulnerability in an air-gapped test environment. Organizations using systematic vulnerability management should calibrate Environmental metrics to their asset criticality data.
Supplemental Metric Group
Entirely new in CVSS v4.0, the Supplemental metrics provide additional context without affecting the numerical score:
- Automatable: Can the attack be automated at scale?
- Recovery: How easily can the affected system recover?
- Safety: Does the vulnerability have physical safety implications?
- Value Density: Does the target system contain concentrated high-value data?
- Vulnerability Response Effort: How much effort is required to remediate?
- Provider Urgency: What urgency level has the vendor assigned?
These metrics are particularly valuable for incident response teams and risk committees who need business context beyond a numerical score.
Key Differences Between CVSS v3.1 and v4.0
| Aspect | CVSS v3.1 | CVSS v4.0 |
|---|---|---|
| Metric Groups | Base, Temporal, Environmental | Base, Threat, Environmental, Supplemental |
| Scope | Binary (Changed/Unchanged) | Replaced by separate Vulnerable/Subsequent System impact |
| User Interaction | None/Required | None/Passive/Active |
| Temporal → Threat | Exploit Code Maturity, Remediation Level, Report Confidence | Simplified to Exploit Maturity |
| Supplemental Context | Not available | Automatable, Recovery, Safety, Value Density, etc. |
| Score Nomenclature | "CVSS Score" | CVSS-B, CVSS-BT, CVSS-BE, CVSS-BTE (indicates which groups were applied) |
The new naming convention (CVSS-B, CVSS-BT, etc.) is a significant improvement for transparency. When someone reports a "CVSS score of 9.1", you now know exactly which metric groups contributed to that number.
How CVSS v4.0 Impacts Penetration Testing
For penetration testing teams, CVSS v4.0 changes how findings are scored and communicated:
- More granular severity ratings reduce the clustering of findings at CRITICAL, making report prioritization more actionable.
- Threat metrics allow pentest reports to reflect whether a discovered vulnerability has known exploits, adding real-world context to technical findings.
- Supplemental metrics like Automatable and Safety help communicate business risk to non-technical stakeholders.
Practical Recommendations
- Update your scoring tools: Ensure your vulnerability scanners and management platforms support CVSS v4.0 vectors.
- Calibrate Environmental metrics: Map your asset inventory to CVSS Environmental metrics for accurate organizational scores.
- Leverage Threat metrics: Integrate threat intelligence feeds (KEV catalog, EPSS) to keep Exploit Maturity values current.
- Train your team: Ensure security analysts understand the new metric structure, especially the Vulnerable/Subsequent System distinction.
- Update reporting templates: Adjust penetration testing and vulnerability assessment report formats to include CVSS v4.0 vectors with the new nomenclature.
Conclusion
CVSS v4.0 represents a meaningful evolution in vulnerability scoring. The addition of Supplemental metrics, the elimination of the problematic Scope metric, and the more granular User Interaction values all contribute to more accurate and actionable severity ratings. While the transition from v3.1 requires updating tools and processes, the improved precision in vulnerability prioritization justifies the effort — especially for organizations managing large vulnerability portfolios under regulatory requirements like NIS-2 or ISO 27001.
For the full specification, refer to the CVSS v4.0 Specification Document published by FIRST.