Continuous Vulnerability Scanning
To build enduringly secure applications, application security must be a focus of every release. By testing early in the development process, development teams can close security gaps before they reach your customer. This increases the quality of the software and reduces costs.





CONSTANTLY HIGH SECURITY LEVEL
Automatic Identification of Attack Vectors in Agile Development Cycles
By quickly integrating our platform into the development cycle as part of a DevSecOps solution, a consistently high level of security can be achieved.
Classify Your Attack Areas
Classify Your Attack Areas
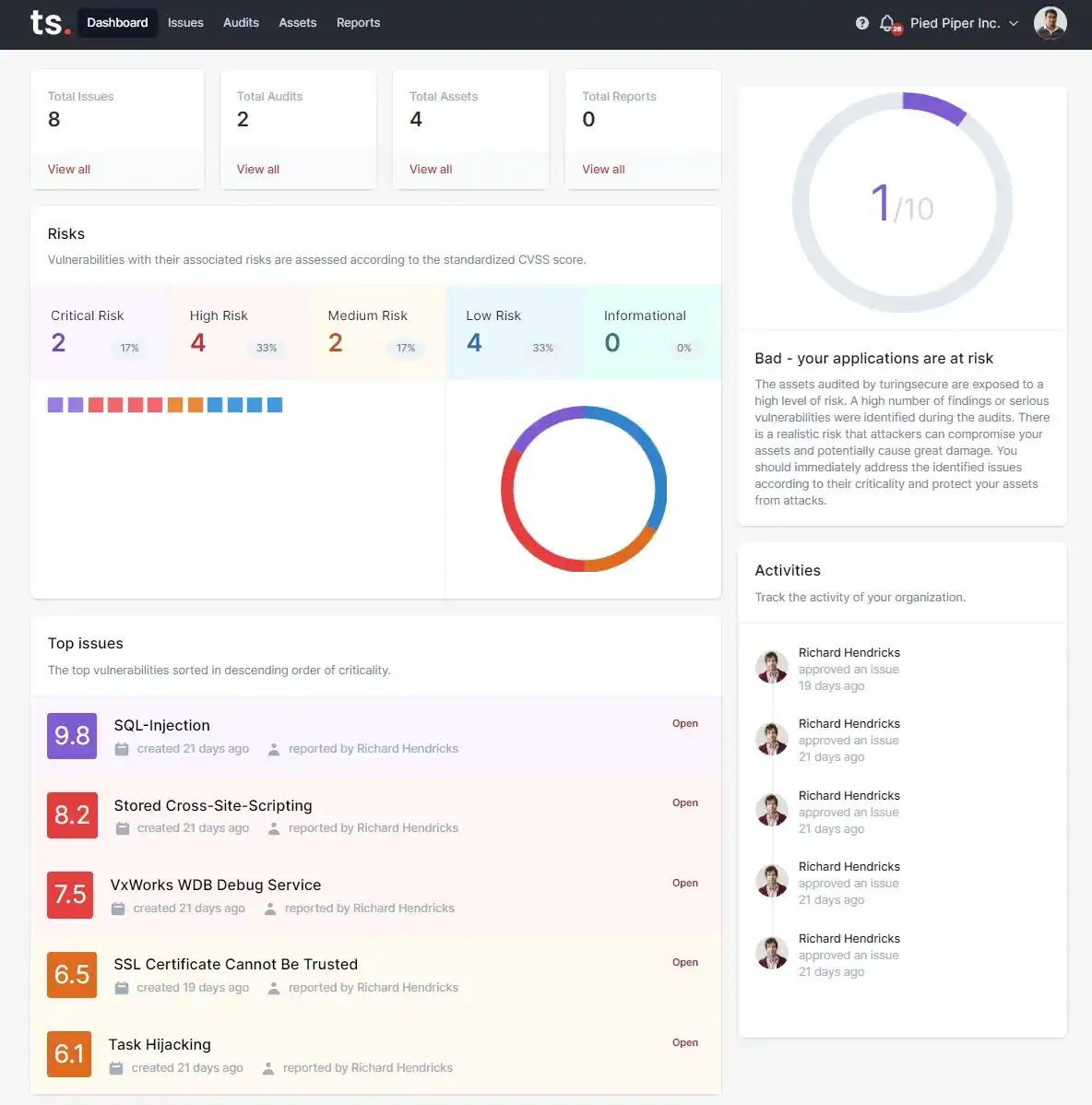
Dynamic inventory of external IT assets and their vulnerabilities in a management board. Monitoring the attack surface is essential for risk management information gathering. Further target-oriented services can be built on this basis.
APPLICATION SECURITY AUTOMATED
Managed Automation Services with High Efficiency
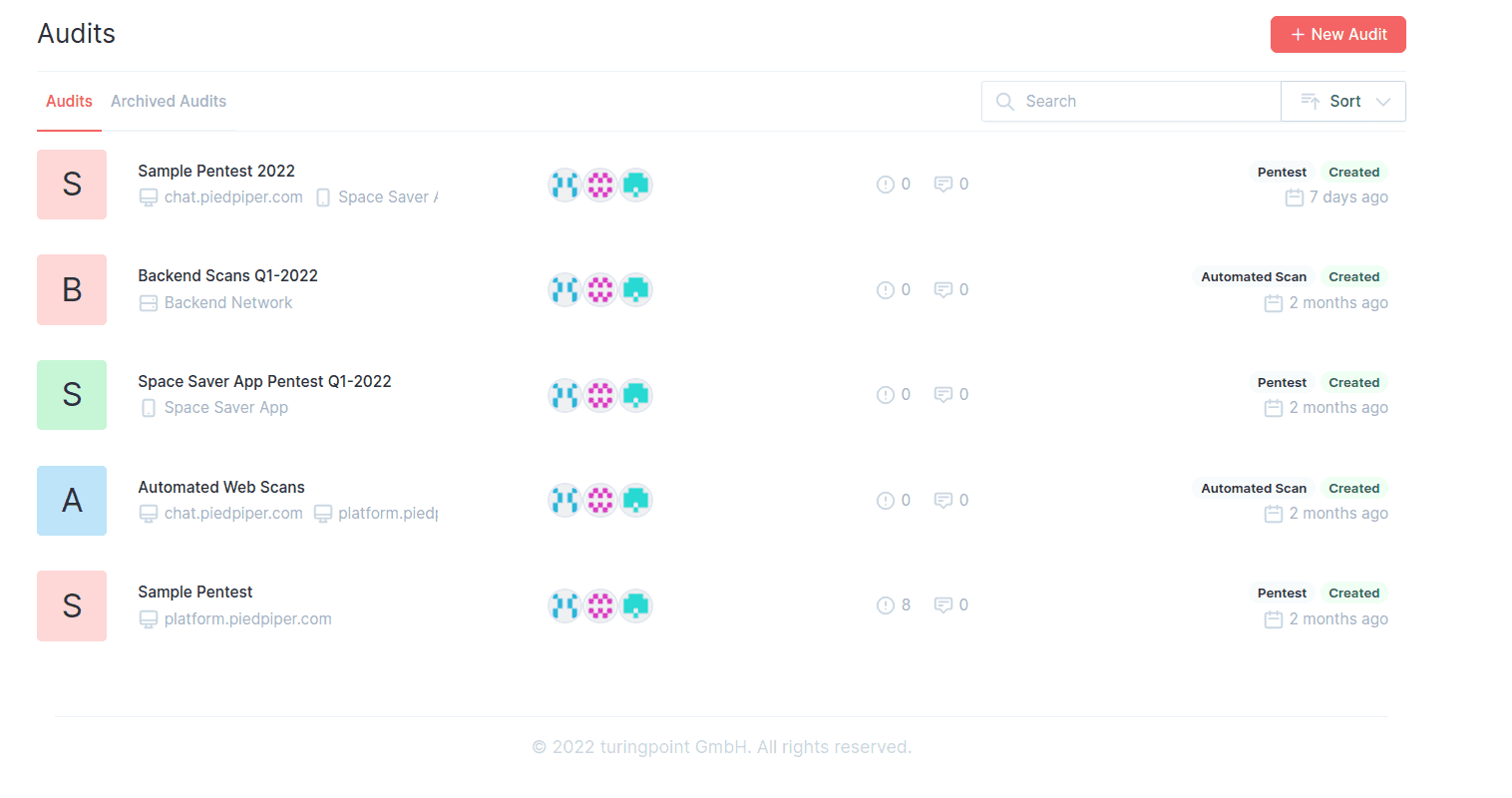
We provide a set of automated security analytics that we manage and that can be augmented by manual activities, such as penetration testing.
DevSecOps Capable Solution Approach
Integration of IT security through event- or time-based security checks in the lifecycle of the application. We guarantee a constantly high level of security through a modern DevSecOps solution.
Individual service level agreements (SLAs) on request
Individual services can be used, which, for example, map recurring services. Often, the business risks are evaluated manually or an incremental penetration test is handled via the platform.
Fast integration into the security development lifecycle
Easy integration and authentication of platform software into the development environment, such as GitHub. Connectivity increases the efficiency and agility of security processes and promotes usability for developers.
Play it Safe 24/7!
Our automated scanners uncover vulnerabilities in web apps, mobile apps, and IT systems before a real hacker can exploit them. Reduce remediation costs, network downtime, and preserve your company's image with the customer loyalty that comes with it.
DEVSECOPS PLATFORM
Automated IT Analyses with a System
Arrange a free consultation with our security experts now!
- Proven processes and trained experts
- Benefit from many years of experience! Penetration tests are planned, performed and evaluated by our specially trained security engineers according to recognized standards. In this way, we master the order-specific requirements every time and flexibly master new challenges.
- Reports that really help
- The final report is the tool for your company to plan efficient security measures and close security gaps. It provides a guideline for investments in IT security and is thus the basis for sustainable security.
- Protect architecture permanently
- There is no such thing as absolute security, because software is constantly evolving. With regular checks, we lay the foundation for lasting security of your architecture.
- Certification for your company
- Our pentest creates a double added value. Besides more security for your system, we have developed an effective certification system. The certificate can be integrated directly into your website and sends a clear message to your customers: "You are safe with us!"
Curious? Convinced? Interested?
Arrange a no-obligation consultation with one of our product experts today.







